About Cognivanta Labs
Building autonomous security infrastructure through cognitive AI and advanced robotics.
Building autonomous security infrastructure through cognitive AI and advanced robotics.
Cognivanta Labs develops autonomous systems for critical infrastructure protection. Our focus is building platforms that can operate continuously in challenging environments where security failures have severe consequences.
We combine aerospace engineering, robotics, and artificial intelligence to create systems that go beyond surveillance tools. Our platforms make autonomous decisions, coordinate as fleets, and operate persistently without constant human oversight.
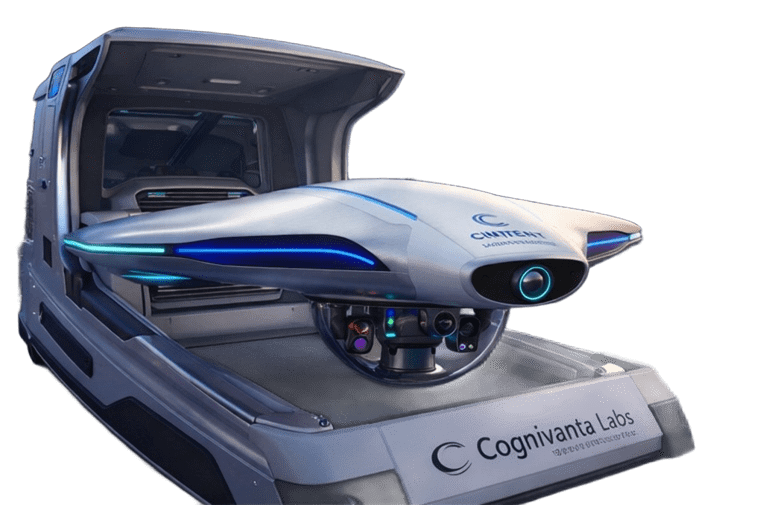
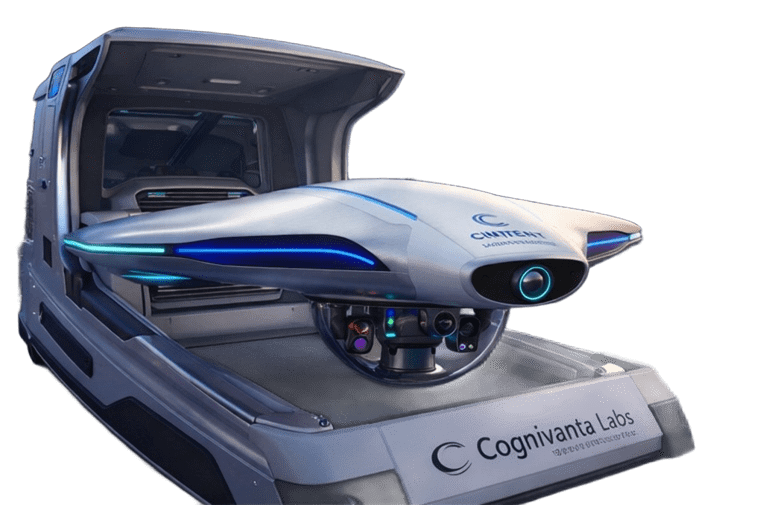
CHAXU is our autonomous aerial security platform. It represents years of development in autonomous flight systems, sensor integration, and cognitive AI for security applications.
The platform addresses a fundamental problem in security operations: traditional systems require continuous human control, limiting their effectiveness for 24/7 protection of large facilities.
CINTENT is our cognitive AI platform that enables autonomous systems to perceive environments, understand context, and make appropriate decisions in real time.
Unlike reactive automation that follows fixed rules, CINTENT processes multi-modal sensor data to build contextual understanding of situations. It identifies deviations from normal patterns, classifies threats based on behavior, and executes appropriate response protocols.
The platform learns from operational experience across deployed fleets, continuously improving threat detection accuracy and reducing false alarms.
CINTENT combines computer vision, behavioral analysis, and decision-making frameworks specifically designed for security applications.
The system operates on edge computing hardware deployed on each aerial unit, enabling autonomous decision-making even during network connectivity loss. This architecture ensures units can continue operations and make critical decisions without reliance on cloud infrastructure.
Fleet-level intelligence sharing allows units to learn from each other's experiences and coordinate responses to complex security scenarios.
We design for the harsh conditions found in refineries, ports, and industrial facilities. Systems must operate in extreme temperatures, high humidity, dust, and adverse weather.
This requires ruggedized components, environmental protection, and redundant systems. Consumer drone approaches do not meet these requirements.
True autonomy means systems can operate for extended periods without human intervention. This requires more than autopilot features.
Our platforms handle patrol planning, threat assessment, charging management, and coordination with other units. Humans monitor and set parameters, but routine operations require no control input.
Systems protecting critical infrastructure must themselves be secure. We implement end-to-end encryption, tamper detection, secure boot verification, and comprehensive audit logging.
Integration with existing security infrastructure is designed from the start, not added later. APIs and standard protocols enable deployment alongside PSIM and VMS systems already in use.
Security systems must function when needed. We prioritize reliability through redundant systems, predictive maintenance, and extensive testing in operational conditions.
Our platforms undergo environmental testing, endurance validation, and failure mode analysis before deployment. Field reliability data feeds back into design improvements.
Autonomous systems operating near personnel and infrastructure must have robust safety mechanisms. We implement multiple layers of collision avoidance, geofencing, emergency protocols, and manual override capabilities.
The enclosed ducted-jet design eliminates rotor strike hazards present in traditional drone architectures, enabling safer operation in industrial environments.
Real deployments face network latency, GPS denial, sensor occlusion, and adverse weather. We design systems to maintain functionality despite these limitations.
Edge AI processing, visual-inertial navigation, and sensor redundancy ensure continued operation when ideal conditions do not exist.
Organizations have existing security infrastructure. Our platforms integrate with established systems rather than requiring wholesale replacement.
We support industry-standard protocols, provide comprehensive APIs, and work with common security management platforms deployed in enterprise environments.
We work with organizations responsible for ports, refineries, power plants, and other facilities where security failures have significant consequences.
These organizations require systems that can operate continuously, integrate with existing security operations, and meet regulatory requirements for critical infrastructure protection.
Government agencies and defense organizations deploy CHAXU for facility security, installation protection, and mission-specific requirements.
We provide classified variants meeting government security standards and work through authorized procurement channels for defense applications.
Site assessment, deployment planning, installation, integration with existing systems, and operator training are all part of our implementation process.
We work with your security team to ensure CHAXU integrates effectively with operational procedures and existing infrastructure.
Technical support, preventive maintenance, software updates, and system optimization continue after deployment.
Our support team provides remote diagnostics, troubleshooting assistance, and rapid replacement of failed components to maintain operational availability.
CINTENT models improve through fleet-wide learning. Software updates deliver enhanced threat detection, reduced false alarms, and new capabilities to deployed systems.
Operational data from your deployment contributes to system improvements that benefit the entire customer base.
We are clear about what our systems can and cannot do. Autonomous security platforms are powerful tools, but they have limitations and appropriate use cases.
We work with customers to determine if CHAXU is appropriate for their specific requirements and environment. Not every facility needs or benefits from autonomous aerial security.
Autonomous systems for security applications require careful consideration of safety, privacy, and appropriate use.
We build systems with human oversight, configurable rules of engagement, comprehensive audit trails, and strong security controls. These are not negotiable features but core requirements.
Deploying autonomous security infrastructure is not a transaction but an ongoing relationship. We are committed to supporting systems throughout their operational life.
This means continued technical support, regular software updates, training as teams change, and working together to adapt systems as requirements evolve.
We bring expertise in autonomous systems and AI, but our customers understand their facilities and security requirements better than anyone.
Effective deployments come from collaboration between our technical teams and your security personnel. We listen to operational needs and design solutions accordingly.
Contact our team to discuss your facility's security requirements and whether autonomous aerial infrastructure is appropriate for your application.